This is an old revision of the document!
KeyCloak
Here's a video showing how SSO based on Keycloak can be used.
- Install, configure and run KeyCloak: https://www.keycloak.org/docs/latest/server_installation/index.html
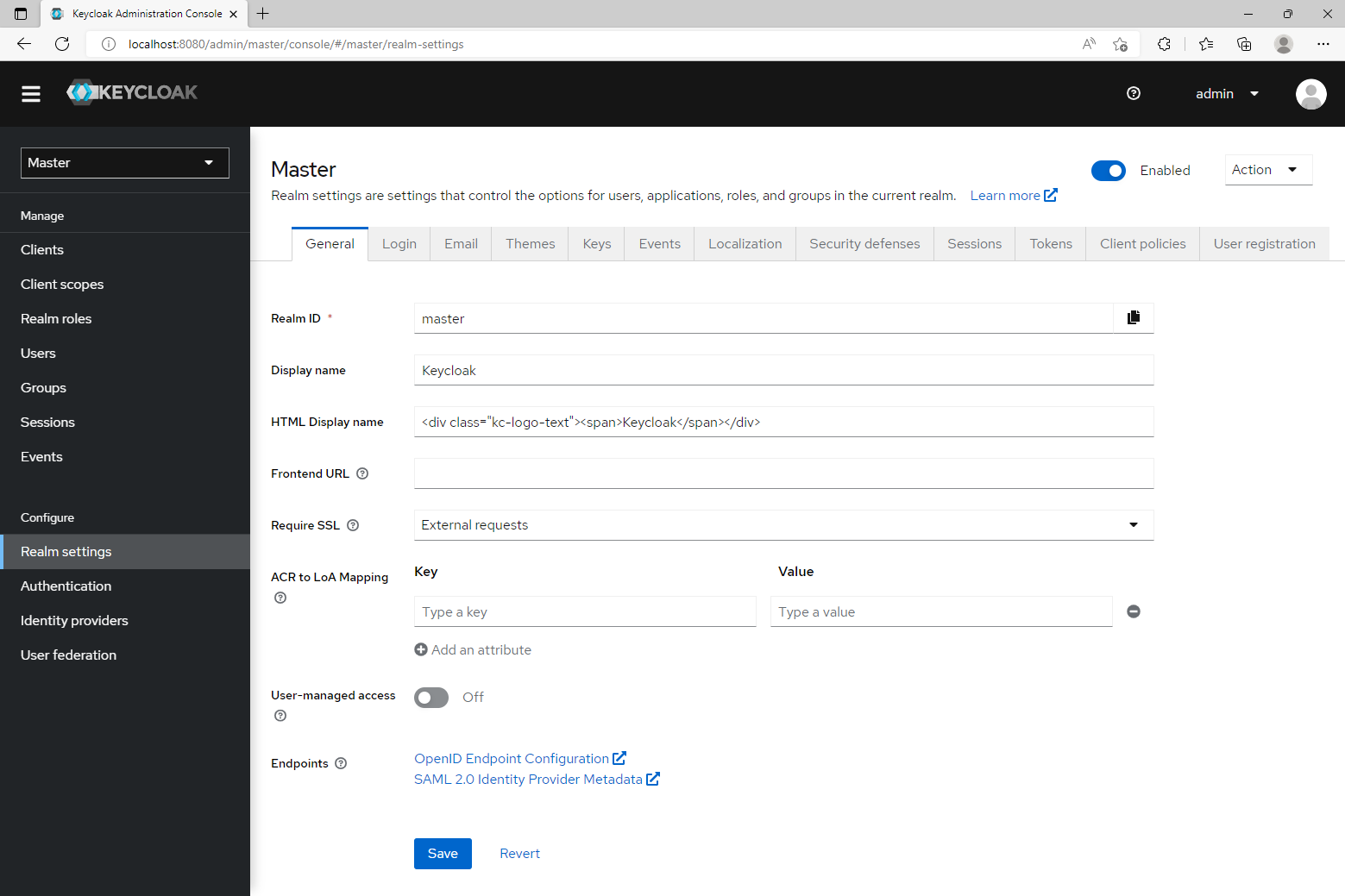
- Login to the admin pages of KeyCloak.
- Click the "Clients" button in the sidebar menu and add a new client by clicking the "Create" button in the top right corner.
- Give it a name and select "openid-connect" as the Client Protocol.
- On the settings page of your new client, add "[BLOCKS-IP]/rest/auth/*" as a "Valid Redirect URI" and set "Access Type" to "confidential", save your changes.
- Select the "Credentials" tab at the top of your client settings page and note the "Secret" for use as [CLIENT-SECRET] in step 1 of the Blocks specific section below.
- Click the "Roles" button in the sidebar menu. Click the "Add Role" button and add the role "Admin". Repeat the process until you end up with the following roles listed:
- Admin
- Manager
- Creator
- Editor
- Contributor
- Staff
- Click the "Users" button in the sidebar menu. Click the "Add user" button in the top right corner and add your first user. On the edit page for the newly created user, select the "Role Mappings" tab at the top and assign the roles you want this user to have.
Blocks specific steps
- Open your Blocks configuration file on your Blocks server and add the "auth" section below to the already existing "server" section. Replace the values of [BLOCKS-IP], [KEYCLOAK-IP], [REALM-NAME], [CLIENT-ID] and [CLIENT-SECRET]. If you didn't configure your own realm for your users, [REALM-NAME] is the default "Master" realm. [CLIENT-ID] is the name of the client from step 4 in the section above.
server: auth: urlResolver: null ajaxRequestResolver: null callbackUrl: https://[BLOCKS-IP]/rest/auth/callback rolesOwner: claims rolesPath: realm_access.roles clients: - org.pac4j.oidc.client.OidcClient: configuration: discoveryURI: [KEYCLOAK-IP]/auth/realms/[REALM-NAME]/.well-known/openid-configuration clientId: [CLIENT-ID] secret: [CLIENT-SECRET] clientAuthenticationMethod: client_secret_basic scope: openid profile groups servlet: security: - matchers: internalMatcher clients: OidcClient authorizers: isAuthenticated
- Start Blocks and go to "/edit" for login.
Role Mapping
If the roles you've added to KeyCloak does not match the roles used by blocks, or if you have set up roles on KeyCloak already and would like to re-use them, you can add role mapping to the Blocks configuration file. You do this by defining a server.auth.rolesMapping parameter where the keys are the roles of your KeyCloak configuration and the values the roles Blocks know about. For example:
rolesMapping: KeyCloakAdmin: Admin KeyCloakManager: Manager KeyCloakCreator: Creator KeyCloakEditor: Editor KeyCloakContributor: Contributor KeyCloakStaff: Staff